
Tripwire Industry Solutions
Automate IT compliance, protect sensitive data, and eliminate outages

Overview:
An increasing number of external forces mandate effective information security in the IT environment across industries. Payment Card Industry Data Security Standard (PCI DSS), Sarbanes-Oxley (SOX) Act of 2002, North American Electric Reliability Corporation (NERC), Health Insurance Portability and Accountability Act (HIPAA), and emerging privacy laws are just a few examples of regulatory compliance requirements and policies that have put unprecedented amounts of pressure on information security management, and specifically on the Chief Information Security Officers (CISOs) to demonstrate that effective controls exist to adequately secure IT systems and data.
Each industry has its own unique list of challenges and risks to data security. Tripwire delivers a robust Automated IT Security and Compliance solution to overcome these unique challenges for all types of organizations-from government agencies or public school systems to privately owned businesses.
Federal Government Cyber Security:
CONNECT SECURITY TO THE MISSION WITH TRIPWIRE
Federal agencies are under pressure to improve cybersecurity by focusing on compliance and risk management initiatives such as continuous monitoring, Federal Information Security Amendments Act (FISMA) compliance, NIST and agency standards. Tripwire delivers the most robust suite of security controls for asset, vulnerability, configuration and risk management requirements, providing security intelligence and evidence of compliance to agency operations. Tripwire helps agencies prioritize critical assets across the network and implement a framework of foundational security controls to continuously monitor information assets to improve risk posture.
Transform Your Controls for Continuous Monitoring
Tripwire solutions transform the static security control assessment process into an automated security information collection process, enabling continuous risk assessment and compliance. Federal security directives require agencies to continuously monitor their systems for cyberthreats and implement regular threat assessments. This focus on risk monitoring and analysis improves the overall posture, awareness and responsiveness of security programs.
Achieve and Maintain Continuous Compliance
Tripwire helps government agencies identify, classify and mitigate vulnerabilities and automate compliance and audit reporting. Tripwire automation for security risk management integrates with continuous compliance goals and reduces time and effort for Certification and Accreditation (C&A). Tripwire solutions are designed to support the reporting and monitoring requirements of FISMA regulations, CyberScope reporting, FDCC and USGCB, DISA STIGs, and supports key security program management. Tripwire has a track record for building best-in-class technology, meeting Federal compliance requirements and integrating standards such as FIPS 140, Common Criteria and SCAP.
Deliver the First Four SANS Critical Security Controls
Federal agencies have begun using the SANS 20 Critical Security Controls (CSC) because it provides continuous monitoring, sequences IT control implementations, and understands budgets and impacts of these implementations. As these controls map to NIST 800-53, the SANS program is promoted by the OMB and DHS as the roadmap for continuous monitoring. Tripwire products help your agency achieve the goals of that roadmap by contributing to 16 of the 20 SANS CSC. Tripwire solutions fully address the four most foundational controls for visibility (inventory of hardware and software) and reducing the attack surface (security configuration & vulnerability management), which are shown to reduce risks and assure an effective defense against current and future cyberthreats. The data from these processes is essential for proper implementation of other controls such as application software security, boundary defense, and security audit logging.
Tripwire Features and Benefits
Tripwire is a vendor of market-leading security products with deep experience in Federal environments. We understand the dynamics in cyberthreats and vulnerabilities, Federal initiatives, and compliance standards. Our products collect data from a large number of operating systems, applications and devices; the products can be integrated into enterprise systems and processes to assure proper scalability and interoperability.
Non-stop Security with System State Intelligence
- Discover, profile and scan every asset on your network for situational awareness
- Identify and prioritize risks based on vulnerabilities & configurations
- Baseline to detect and update changes and compare to standards (e.g.FISMA, NIST, DISA, NSA)
- Provide context to make SIEM, Help Desk and GRC tools useful to detect security breaches as they happen
Monitor the Extended Enterprise
- Single flexible solution for enterprise view of servers, databases, firewalls, network devices, directory services, applications and workstations
- Interoperable with other products such as help desk, asset management, configuration management, and incident response solutions
- Support compliance with applicable Federal laws, Executive Orders, directives, policies, regulations, standards, and guidelines with industry's largest policy content library
Reduce Program Costs with Security Automation
- Fully automates checks for patches, vulnerabilities, misconfigurations and unauthorized changes
- Leading the way in development of security technology developed in accordance with latest SCAP 1.2 standards
- Provides top-to-bottom drilldown capabilities from general scoring trends and rollups to specific test failures and remediation checklists
Managed Service Providers:
Secured by Tripwire
IT Security & Compliance for Cloud Computing & Managed Services
Before customers entrust their IT needs to your managed or cloud services, they need assurance that your infrastructure is secure and compliant along with visibility into their own security and compliance. The Secured by Tripwire program provides you with the technology and support needed to move your customers into the cloud with confidence.
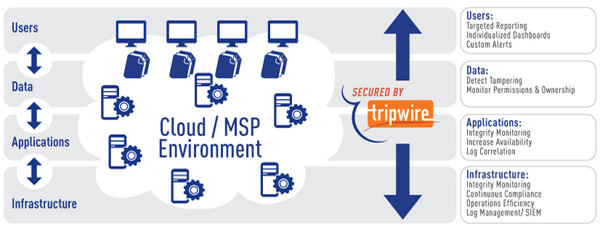
Secured by Tripwire is backed by the Tripwire® VIA™ platform, an integration of industry-recognized file integrity monitoring, compliance policy management, log management and SIEM solutions. The platform helps ensure the security and compliance of your infrastructure with powerful incident management capabilities, immediate alerts about suspicious activities, and access to detailed forensic data. The program also gives you all the components required to deliver your customers the compliance and security reports and dashboards they demand. This lets you address your customers' security concerns and gives them proof of compliance in the cloud.
Secured by Tripwire Benefits for Managed Service & Cloud Providers
In the spirit of the cloud, Secured by Tripwire offers true, elastic pricing so your total cost of ownership remains low. You pay only for what your customers use, when they use it. Tripwire ensures your success by providing you with technical and marketing support as part of the program.
With Secured by Tripwire, you get the following benefits:
- Automated, Continuous Compliance
Automate monitoring, reporting and remediation against regulatory compliance and security standards, including PCI, FISMA, GLBA, HIPAA and NERC. - Proven IT Security & Compliance
Ensure that your infrastructure stays secure and compliant with a service based on the Tripwire VIA platform, including its robust reporting and remediation capabilities. - Increased Efficiency & Control
Rely on the Tripwire VIA platform to efficiently scale, standardize, and automate the delivery of security and compliance information for your customers, integrating easily with other management tools. - Support for Success
Count on Tripwire to provide the technical and marketing support you need to successfully launch your compliance and security services offering. - Market Differentiator & New Offering
Easily deploy new managed compliance and security services, accelerate your revenue growth, enter new markets, and differentiate your offerings. - Rapid Deployment of Compliance
Quickly offer a packaged set of compliance services to customers such as example reports, dashboards and other evidence, or provide customized offerings around unique customer requirements. - Flexible, Elastic Licensing & Pricing
Pay for only what your customers use with elastic licensing and pricing options. Minimize your upfront costs and maximize your margins.
UK Public Sector:
Minimise Costs and Protect Against Cyber Threats with Protective Monitoring
Along with terrorism, cyber attack was recently identified as the most serious threat facing the UK. Cyber-crime has been estimated in the billions per year globally, with untold human cost, as British shoppers spent £4.4 billion online during August 2010. But the highest priority concerns do not always mean additional resources. Senior Information Risk Officers (SIROs) need to maximise ICT investments to implement Protective Monitoring to reduce cyber security risk.
The Tripwire® VIA™ suite combines the power of Tripwire® Log Center—log and SIEM—with the intelligence of Tripwire® Enterprise—FIM and configuration control—providing intelligent information to act quickly and effectively to address new and evolving threats to our security. Tripwire VIA solutions help you spot emerging risks before they become crises, and meet the compliance requirements like Good Practice Guide (GPG) 13, GSCX Code of Connections (CoCo), Payment Card Industry (PCI), Public Sector Network (PSN), Data Protection Act (DPA), and Community Security Policy (CSP).
Gain situational awareness of events of interest to affordably meet compliance requirements and use Protective Monitoring requirements to reduce your cyber security risk.
UK Public Sector Compliance Policies
Gain situational awareness of events of interest to affordably meet compliance requirements and use Protective Monitoring requirements to reduce your cyber security risk.
- GPG 13 » SPF » GCSX COCO » ISO 27001/2
